StaffCounter update for Windows 10 Defender PUA
For the last year, cyber-criminals succeeded in a few significant cyber attacks by using weaknesses in Windows operating system, and so-called “supply chain” attack approaches. As a response, since September 2021, for the latest Windows 10 version (20H2), Microsoft turned ON by default protection against potentially unwanted apps (PUA) by blocking them when a user is downloading a setup file. Windows defender incorrectly flagged Staffcounter Setup as PUA due to functionality like screenshots, screen reading, and keylogging. At the same time, Symantec EndPoint protection also labeled the SafeJKA code signature as the “WS.Reputation” flag. We have submitted an application of False-Positive detection to both organizations. To change the StaffCounter reputation level in Windows Defender cloud-based Threat intelligence, we also have released an extra update.
For now, we assure you it is absolutely safe to install the StaffCounter Setup file. If you encounter difficulties downloading the setup file
- use the “Allow on this Device” option in the Windows Threat protection dialog.
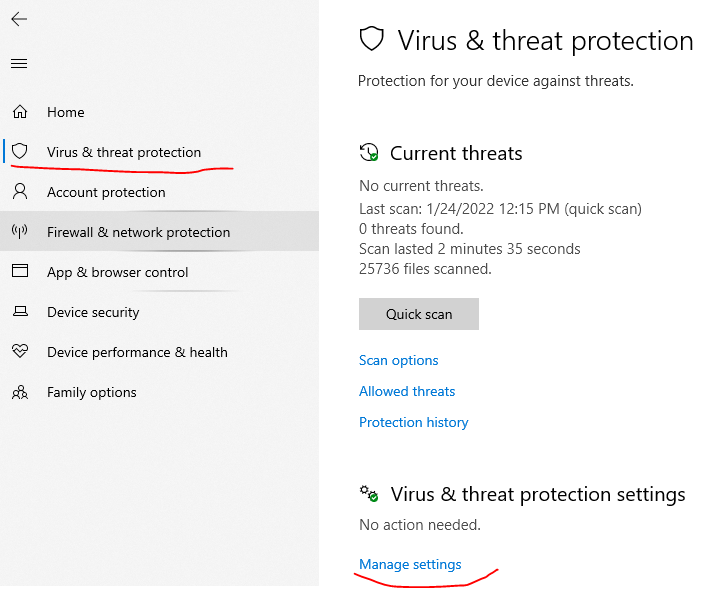
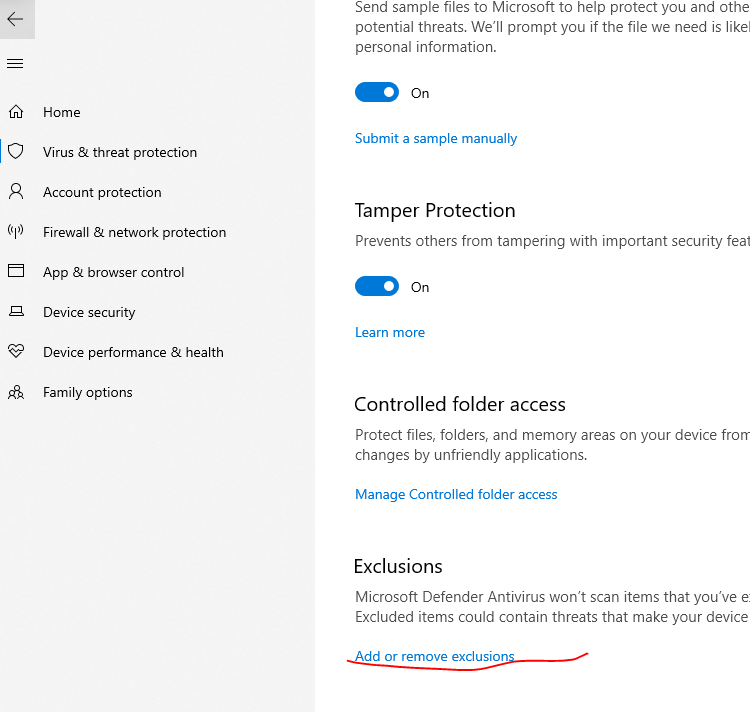
- add 2 folders to the list of exclusions of the Windows Security Service – Program files (x86) and Downloads
Or add exception via command line:
powershell -inputformat none -outputformat none -NonInteractive -Command “Add-MpPreference -ExclusionPath ‘C:\Program Files (x86)\StaffCounter'”
scroll down and click on “Add or Remove exclusion”
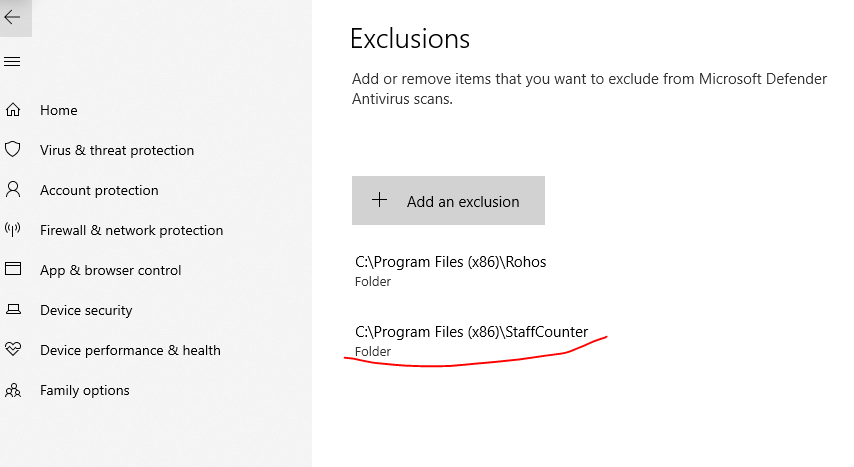
Now verify that folder “C:\Program Files (x86)\StaffCounter\” is listed in the list below –
Potential Unwanted Apps
Potential Unwanted Apps (PUAs) are not considered malware, but they can be harmful in other ways. These apps typically include adware and other unwanted programs that accompany apps that you download from the internet. An application that bundled with a 3rd party less trusted software or unsigned modules is also considered as PUA according to Windows Threat Intelligence to avoid the potential risk of “supply chain” attacks caused by software components without code signature.
Some potentially unwanted apps (PUAs) mostly come bundled with the primary app downloaded by the user, and they’re not necessarily dangerous. According to Microsoft, these apps are also considered PUAs: Adware, Torrent (Enterprise PCs only), miners, bundling software, marketing software, and apps with poor industry reputation. Many software vendors such as Parental Time Control, Employee Monitoring, and time-tracking systems received PUA flags automatically due to the presence of screenshotting, keylogging, and screen-reader features. Artificial Threat Intelligence (AI) algorithms in Windows Defender cloud consider these features as potentially dangerous or “unwanted”.
Secure software development and operations -DevSecOps
During the last year, we at SafeJKA company make more efforts to change internal software development and distribution practices to deliver safe software products.
- Company IT infrastructure changed to be more plain and flat, omitting dependencies from centralized systems like Windows Active Directory where it is not needed.
- Additional secure development practices were introduced on software developers’ computers.
- Setup package release is done on a separate virtual environment.
- All external software components have been rebuilt from source code and digitally signed.
- Some external software packages are used in a separate virtual environment with alternative safeguards like AV of other brands. Some software has been rebuilt from the source code.
- Code signature for all binaries by SafeJKA SRL code signing certificate.
- Constant integrity monitoring of release distribution host.