StaffCounter DLP – effective monitoring and enterprise security
This material will be useful for directors and HR managers.
Introduction
All of us have ever been deceived. And even betrayed. Unfortunately, we are often surrounded by people who put their personal interests above honor and conscience. In our case, we will talk about subordinates – employees. The prosperity and development of any business depend on them. Perhaps they are not to blame, perhaps their life forces them to act as they do. Perhaps they can still be re-educated? Let’s try! After all, their professional skills are very important for us!
We start with control
First, let’s cure their laziness. Knowing that everything they do is under control will help them think less about extraneous things at work. They will pay more attention to work, and may even be carried away by it. The easiest way is to install the tracking program directly on the employee’s computer so that it can discreetly record all his actions and send them to the server. Our StaffCounter DLP does just that. On the server, this information is processed, sorted into useful and useless categories, and provided to the manager or director for control. The duration of breaks and being late for work is recorded. It is enough to tell the employee once when and how distracted he was, what programs he launched, and what sites he viewed so that his work would go much faster and more efficiently.
Read more about the StaffCounter monitoring program.
In the new version of the program, we have added an extended control panel, the ability to record sounds around the computer and record the text written by an employee.
To launch the program control panel, open the Settings page on the server and select the required department.
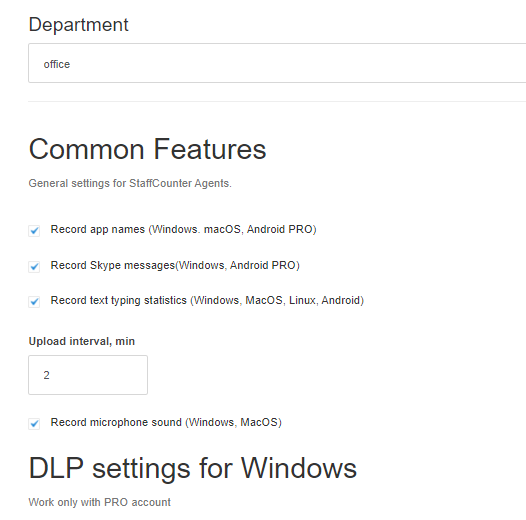
Here you can activate the recording of ambient sounds. (Record microphone sound (Windows, macOS)). Sounds are not recorded all the time, but when a certain volume threshold is reached. To adjust this threshold, set the Sound threshold level field in the range of 1-100. The lower the value, the more sounds will be recorded and the longer the audio file will be.
The Interval between screenshots, min parameter allows you to set the minimum interval between screenshots in minutes. A value of 0 will mean no screenshots at all, to save server space. The same applies to webcam snapshots.
The second step is an enterprise security
Information security is as vital to the operation of every business as the efficiency of every employee. Therefore, we have built into the StaffCounter DLP program the functions of restricting the launch of certain programs, the use of DVDs and removable media, as well as access to network resources. All this can be used to “drain” information about the company, its activities, and transfer important documents to competitors. Our module is called DLP (Data Leak Prevention).
The “DLP settings for Windows” section allows you to enable or disable insider protection features. In the working folder of the Staffcounter program on the employee’s computer, there is a text document dlpcfg.ini, which is the configuration file of this program module. Having changed this file, you should save it and enable some item in the DLP section
The rules for editing the configuration file are simple:
– comments must begin with a “;”
– parameters should not be commented out
– after the “=” sign, you can enter only the admissible values specified in the comments before the parameter
– parameters cannot be rearranged in places
Let’s go through the parameters. They are divided into several sections:
[Main] section
DisableUsbMtp – Disable access via MTP-protocol (cameras, some phones, etc.) Possible values: 1/0. The function does not allow users to transfer data to phones, cameras, players, and other devices connected via the USB port. Devices are unavailable for reading and writing.
DisableDvdWrite – Disable DVD burning. Possible values: 1/0. The program prohibits writing to CD and DVD directly from the explorer, as well as through various burning programs.
DisableNewBluetoothConnection – Deny the connection (pairing) of new Bluetooth devices. If no Bluetooth devices have been paired with the PC, then this option prohibits working with any Bluetooth. Possible values: 1/0.
EnableUsbRules – Enable UsbMassStorage control. Possible values: 1/0. Requires clarification in the [UsbRules] section. This function, depending on the settings in [UsbRules], can completely deny access to removable USB drives, open them read-only, or prohibit or allow writing to media with a specific serial number, PID, and VID values.
EnableNetControl – Enable access control to network resources. Possible values: 1/0. Requires clarification in the [NetRules] section. Allows you to deny access to all networked computers, or selectively allow or deny access to specific machines based on their network name.
DisableWindowsNetShare – Full locked to standard network access (works MUCH faster than EnableNetControl). Does not depend on the state of EnableNetControl. Possible values: 1/0.
DisableNostdNetShare – Denying non-standard network access. Network access set up by 3-rd party programs. For example, this access uses VirtualBox to access its public folders. Does not depend on the state of EnableNetControl. Possible values: 1/0. Perhaps this option will be useful when using the program in a virtual machine.
DisableExecuteFromNonFixed – Disable starting from non-Fixed disks. Possible values: 1/0. applies to -exe and -bat files. Will not allow the user to run a program that he brought on a USB flash drive or optical disk.
EnableProcessControl – Enable process control. Possible values: 1/0. Requires clarification in the [ProcessRules] section This parameter enables the ability to control the operation of other programs. In particular, in the [ProcessRules] section, you can write rules for various programs, prohibiting the launch of some and restricting access to files of other programs. The latter can be useful for preventing the transport of data through Web browsers or e-mail programs.
DisableExeCreation – Prohibiting the creation of EXE files. Possible values: 1/0. Includes a ban on the compilation, renaming, copying exe-files from removable media.
NoCheckSystemUser – Do not check system accounts (system, local service, network service, etc.). Possible values: 1/0. This option can be useful in combination with other options, for example, with a ban on access to USB drives. In the case of using a USB drive as a hardware key, the System should see it, but the user does not have the right to read or write any information to it.
OutputUsbInfo – Print information about the connected UsbMassStorage to the registry. The information is updated when a new UsbMassStorage is connected. Outputs up to 10 USB
Diagnostics of errors:
LogFile=\??\c:\Tools\dlpflt_package\drv.log – NT-path to the log file (if not specified, the log is not created). The directory in which the file is located must exist. When you restart the program, the file is overwritten
LogLevel=2 – logging level for the driver
List of administrators
Parameter format “name” =% username%
; [Admins] – by default, the administrator is the user who installed and enabled DLP functions. Other users, even administrators, will not be able to change the rules. Consider this when deleting this user account. To activate the section and assign other administrators, remove the “;” before [Admins]
Section [NetRules] – clarifies the EnableNetControl parameter.
Setting example:
deny = WIN8-64 // it is forbidden to log into a network computer named WIN8-64
allow = Server3 // allowed to access a networked computer named Server3
; deny = WIN8 // temporarily disable the ban on logging in from a network computer named WIN8
allow = * // allow access to all other servers. The command with * must go last. If you want to deny access to all other computers on the network, place the deny = * command at the end of the section
Section [UsbRules] – clarifies the EnableUsbRules parameter
Record format:
% VID%:% PID%:% SN% = rw
where% VID% and% PID% is a 16-bit unsigned integer (decimal or hexadecimal number. Use the 0x prefix to enter the hexadecimal number)
% SN% – serial number (string)
If one of the fields == ‘*’, then it can be arbitrary
Example:
[UsbRules]
123: 0x123: 123456001 = rw;
where
VID = 123, PID = 291 (0x123), SN = “123456001”; Read and write allowed.
123: 0x123: 123456002 = r; Read-only allowed.
123: 0x123: 123456003 =; Access is denied.
0x90C: *: * = rw; For VID = 2316 (0x90C) and arbitrary PID and SN. Read and write allowed.
*: *: * =; Default rule (for all others). Reading and writing are prohibited.
Attention: the ‘r’ parameter does not prohibit deleting data from a USB drive.
[ProcessRules] section – clarifies the EnableProcessControl parameter in the [Main] section
The description of the rule for each program must begin with the newrule field
All fields up to the next newrule refer to this process
newrule = ~~~~~~~ Program_name ~~~~~~~~; The beginning of a new rule. The field value can be arbitrary.
imagePath =% PathToExeFile%; Exe-file path (NT-path. Wildcard (? *) Can be used)
allow | deny =% MinSize%:% Path%; Control rule. % Path% – NT path. Wildcard can be used (? *)
allow | deny = *; Default rule
allowExeCreation = 1; Disables the check for EXE creation for this process (with DisableExeCreation = 1)
Example: preventing Calculator from using files outside of the Windows directory
[ProcessRules]
newrule = —— calc —————-
imagePath = * \ Windows \ System32 \ calc.exe – file path
allow = 0: * \ Windows – in this case, 0 means the minimum file size in bytes, at which the rule takes effect (you can use all files from the Windows folder)
deny = * – it is forbidden to use everything else.
An example for the UCBrowser program:
newrule = ——– UCBrowser ——–
imagePath = * \ Program Files (x86) \ UCBrowser \ Application \ UCBrowser.exe; program location
allow = 0: * \ Windows \ *
allow = 0: * \ AppData \ *
allow = 0: * \ Roaming \ *
allow = 0: * \ UCBrowser \ *
allow = 0: * \ ProgramData \ *
deny = 100: *
allowExeCreation = 0
allow = *
In this example, the UCBrowser program is allowed to use all files and folders from the Windows, AppData, Roaming, ProgramData, UCBrowser directories, it is forbidden to open files over 100kb from other places, it is forbidden to copy files with the EXE and BAT extensions to the computer, and everything else is allowed. Thus, the program will be able to start, find all its necessary components and settings, be able to access the Internet, and display the content of Web pages. However, it will not be able to take files over 100kb in size from non-system directories for transferring to the network, and it will also not be able to download and save executable files on the computer.
How can you protect system directories if the user tries to copy secret information there? For this user, remove administrative privileges and turn off the display of hidden files and folders in his user profile.
Conclusion
The StaffCounter DLP service allows you to effectively protect an enterprise, both from employee dishonesty and from outright encroachment on enterprise secrets. We hope he will become your faithful assistant on your way to success.